Cloud computing has become the cornerstone of modern business operations. Organizations across industries are embracing the cloud's agility, scalability, and cost-effectiveness to power their digital transformations.
However, this reliance on cloud-based infrastructure also introduces new security challenges that demand proactive measures to safeguard sensitive data and applications.
Cyber Threats

Cyber threats are constantly evolving, and cloud environments are prime targets for malicious actors. The dynamic nature of the cloud, with its shared resources and complex configurations, presents a larger attack surface for attackers to exploit.
Data breaches, unauthorized access, and application vulnerabilities are just a few of the threats that can jeopardize cloud security.
Cloud Application Security Testing
Cloud application security testing is a crucial component of a comprehensive cloud security strategy. This process involves identifying and eliminating security vulnerabilities in cloud-based applications before they can be exploited.
By implementing a robust cloud application security testing program, organizations can significantly enhance their cloud security posture and protect their valuable data and applications.
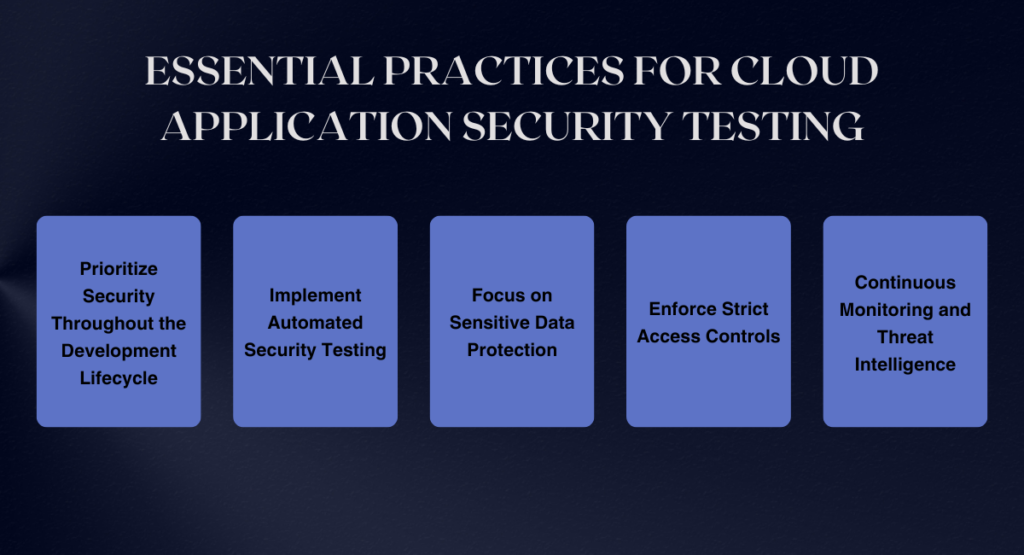
Here are some essential practices for cloud application security testing:
Prioritize Security Throughout the Development Lifecycle:
Integrate security testing into every stage of the development lifecycle, from design to deployment. This approach helps catch vulnerabilities early and reduces the cost of remediation later on.
Implement Automated Security Testing:
Leverage automated tools to perform regular scans and identify potential vulnerabilities. Automated testing can significantly improve efficiency and provide continuous visibility into the security posture of cloud applications.
Focus on Sensitive Data Protection:
Implement robust data protection measures, including encryption at rest and in transit, to safeguard sensitive information from unauthorized access.
Enforce Strict Access Controls:
Implement granular access controls to restrict access to cloud resources and applications to authorized users only. This principle of least privilege ensures that only the right people have access to the right data.
Continuous Monitoring and Threat Intelligence:
Continuously monitor cloud environments for suspicious activity and utilize threat intelligence feeds to stay informed about emerging threats. This proactive approach enables organizations to detect and respond to threats promptly.
Book a Demo and experience ContextQA testing tool in action with a complimentary, no-obligation session tailored to your business needs.
According to recent statistics, cloud security incidents are on the rise. A 2023 report by IBM Security found that data breaches in cloud environments increased by 10% in the past year. This underscores the importance of implementing effective cloud application security testing practices.
Industry experts emphasize the need for a comprehensive cloud application security approach that encompasses technology, processes, and people.
They advocate for a shift from reactive to proactive security measures, emphasizing the importance of integrating security into the development lifecycle and continuously testing and monitoring cloud environments.
Cloud application security testing is an ongoing process that requires continuous vigilance and adaptation. By embracing best practices, organizations can shield their cloud infrastructure from evolving threats and protect their valuable data and applications.
In the dynamic world of cloud computing, security is not an afterthought; it is a cornerstone of a successful cloud strategy.
You may also be interested in: Supercharge Your Testing Capabilities with Automation: Elevate Efficiency, Reduce Time to Market, and Deliver Top-Tier Software
