Master CI/CD Security: The Ultimate Guide for Developers & Ops
Continuous Integration (CI) and Continuous Delivery (CD) are essential practices in modern software development aimed at improving the development and delivery processes. The global market for CI/CD security(Continuous Integration or Continuous Deployment) Tools is expected to experience significant growth between 2023 and 2030. The market is steadily expanding, and the increasing adoption of strategies by key players is anticipated to propel further growth beyond the projected horizon.
- Continuous Integration (CI): CI involves the frequent integration of code changes into a shared repository, where automated tests are run to ensure that the new code integrates successfully with the existing codebase. The primary goal of CI is to detect and address integration issues early in the development cycle, preventing the accumulation of bugs and reducing the time and effort required to fix them.
- Continuous Delivery (CD): CD extends CI by automating the entire delivery process, allowing for the seamless and reliable deployment of code changes to production or staging environments. The ultimate objective of CD is to deliver software updates quickly, safely, and consistently, providing a smooth experience for both developers and end-users.
Common CI/CD Security Challenges
Pipeline Vulnerabilities:
Description:
CI/CD pipelines are susceptible to various vulnerabilities that malicious actors can exploit.
Challenges:
- Insecure Pipeline Configuration: Misconfigured pipelines may expose sensitive information or provide unauthorized access.
- Lack of Pipeline Encryption: Unencrypted communication within the pipeline may lead to data interception and manipulation.
- Insufficient Access Controls: Weak access controls might allow unauthorized users to manipulate or disrupt the pipeline.
Code Repositories and Version Control Security:
Description:
Code repositories and version control systems are prime targets for attackers seeking to compromise source code integrity.
Challenges:
- Insecure Repository Access: Weak access controls on repositories may result in unauthorized code modifications or exfiltration.
- Code Injection: Malicious code injections into repositories can lead to the distribution of compromised code.
- Insufficient Logging: Lack of comprehensive logging can hinder the detection of unauthorized repository activities.
Dependency Management Risks:
Description:
Dependencies, including libraries and third-party components, introduce security challenges due to potential vulnerabilities.
Challenges:
- Outdated Dependencies: Failure to update dependencies may expose the software to known security vulnerabilities.
- Compromised Package Sources: Using compromised or malicious package sources can introduce malicious code into the application.
- Lack of Dependency Scanning: Not scanning dependencies for vulnerabilities can result in the inclusion of insecure components.
Secrets Management in CI/CD:
Description:
CI/CD pipelines often require sensitive information such as API keys, passwords, and tokens, which need secure management.
Challenges:
- Hardcoded Secrets: Embedding secrets directly into code or configuration files poses a security risk if they are exposed or leaked.
- Weak Encryption: Inadequate encryption of stored secrets may lead to unauthorized access.
- Limited Rotation: Failure to regularly rotate and update secrets increases the risk of compromise.
Addressing these challenges requires a comprehensive approach to CI/CD security, incorporating best practices such as:
- Regular Security Audits: Conduct audits of CI/CD configurations and pipeline activities to identify and rectify vulnerabilities.
- Encryption and Access Controls: Implementing robust encryption mechanisms and access controls to protect sensitive information.
- Dependency Scanning: Regularly scanning and updating dependencies to patch known vulnerabilities.
- Secrets Management CI/CD security practices: Utilize secure vaults, rotate secrets regularly, and avoid hardcoding sensitive information.
- Security Training: Providing security awareness training to development and operations teams to ensure a security-first mindset.
By proactively addressing these security challenges, organizations can enhance the resilience of their CI/CD pipelines and better protect their software delivery processes from potential threats and vulnerabilities.
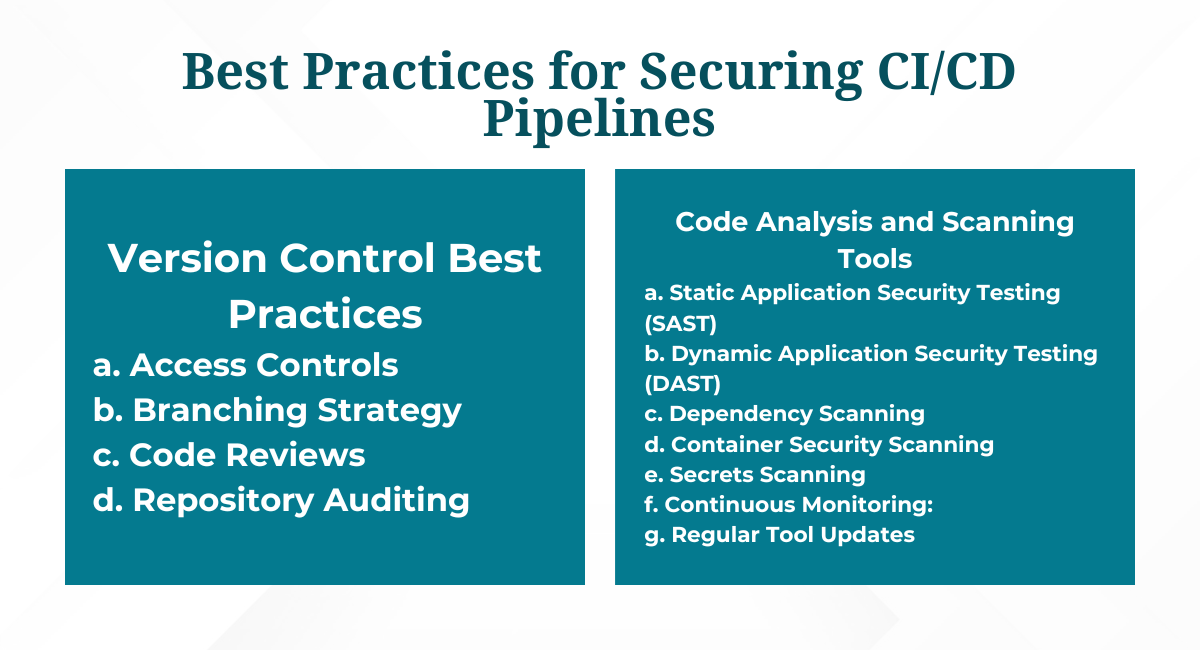
Best Practices for Securing CI/CD Pipelines
Version Control Best Practices:
a. Access Controls:
-
- Implement fine-grained access controls on version control repositories to restrict permissions based on roles.
- Use role-based access control (RBAC) to ensure that only authorized personnel can modify or access sensitive code.
b. Branching Strategy:
-
- Adopt a branching strategy that separates development, testing, and production code.
- Implement branch protections to prevent unauthorized changes to critical branches.
c. Code Reviews:
-
- Enforce mandatory code reviews for all changes to ensure that multiple sets of eyes validate the code.
- Include security-focused code reviews to identify and address potential vulnerabilities.
d. Repository Auditing:
-
- Enable repository auditing to track and log changes, allowing for the detection of unauthorized or suspicious activities.
- Regularly review audit logs to identify and respond to security incidents promptly.
Code Analysis and Scanning Tools:
a. Static Application Security Testing (SAST):
-
- Integrate SAST tools into the CI/CD pipeline to analyze source code for security vulnerabilities without executing the code.
- Set up automated scans to identify and address security issues during the development process.
b. Dynamic Application Security Testing (DAST):
-
- Incorporate DAST tools to assess applications in a runtime environment, identifying vulnerabilities that may arise during execution.
- Integrate DAST scans into pre-production environments to catch security issues before deployment.
c. Dependency Scanning:
-
- Utilize dependency scanning tools to identify and manage vulnerabilities in third-party libraries and components.
- Regularly update dependencies and automate scans to ensure the use of secure and up-to-date components.
d. Container Security Scanning:
-
- Integrate container security scanning tools to analyze container images for vulnerabilities and misconfigurations.
- Implement automatic image scanning as part of the CI/CD pipeline to identify and mitigate security risks.
e. Secrets Scanning:
-
- Implement tools that can scan code and configuration files for hardcoded secrets.
- Integrate secrets scanning into the CI/CD pipeline to identify and remediate exposed or improperly managed secrets.
f. Continuous Monitoring:
-
- Implement continuous monitoring tools to detect and respond to security threats in real time.
- Set up alerts for suspicious activities, unauthorized access, or deviations from secure configurations.
g. Regular Tool Updates:
-
- Keep all security analysis tools current to ensure they incorporate the latest security vulnerability databases and detection techniques.
- Schedule regular reviews of tool effectiveness and consider the integration of new tools as needed.
Real-World Examples: Successful Implementations of Secure CI/CD
Netflix:
Overview: Netflix is known for its robust CI/CD security practices, ensuring rapid and secure delivery of streaming services.
Security Measures: Netflix employs a comprehensive set of automated testing, including chaos engineering, to identify and address potential issues. They use automated canary deployments, allowing them to gradually roll out changes to a subset of users and monitor for any adverse effects before an entire deployment. Robust access controls and encryption mechanisms are in place to protect sensitive data and configurations.
Google:
Overview: Google, a pioneer in CI/CD, has implemented security measures across its extensive software development projects.
Security Measures: Google emphasizes the importance of automated testing at scale, utilizing various testing tools to ensure code quality and security. Continuous integration is a fundamental practice, enabling Google to catch integration issues early in the development process. Google focuses on container security, using tools like Kubernetes for orchestration and Container Analysis for vulnerability scanning.
Facebook:
Overview: Facebook (now Meta) relies on CI/CD security practices to deploy updates to its social media platforms rapidly.
Security Measures: Facebook emphasizes automated testing, including unit tests, integration tests, and end-to-end tests, to maintain code quality and security. The company employs blue-green deployments, enabling the safe rollout of changes by routing traffic between two identical environments.
Security is ingrained in the development culture, with regular security training for developers and the use of automated security tools. As CI/CD security practices continue to evolve, the integration of robust security measures will remain a critical aspect of ensuring the integrity, availability, and confidentiality of software delivery pipelines.
Organizations that prioritize and adapt to emerging trends in CI/CD security will be better equipped to meet the challenges of a rapidly changing technological landscape.
You may also be interested in Automated Regression Testing | Deliver Quality, Effortlessly
Book a Demo and experience ContextQA testing tool in action with a complimentary, no-obligation session tailored to your business needs.
We make it easy to get started with the ContextQA tool: Start Free Trial.